100 Days to Build a Strong Cybersecurity Foundation
A Comprehensive Resource for CISOs on their Cybersecurity Journey
*Now updated for guidance on the SEC Cybersecurity Rules!
CISOs are facing increasing regulatory pressures that are quickly changing their role in the organization. This guide was developed to help CISOs make the most of their first 100 days on the job but is useful for current CISOs who are navigating this new world. Written by CISOs for CISOs, it provides pragmatic guidance on key activities that are critical to cybersecurity program success. And, the updated 2024 guide contains a section dedicated to addressing the SEC’s Cybersecurity Rules—a new program imperative.For both new and seasoned CISOs, we emphasize revisiting and recalibrating core capabilities in 2024, such as
- Relationship building
- Involvement in strategic planning
- Cybersecurity risk management and governance
- Frameworks and metrics
- Incident response
- Risk quantification
Download the guide and make a positive impact in 100 days
The changing landscape for CISOs calls for a recalibration of core capabilities.
The evolution of the CISO’s role and importance in the organization requires revisiting and revising key practices, including identifying and institutionalizing cybersecurity performance metrics and risk quantification to support impact materiality calculations and considerations.
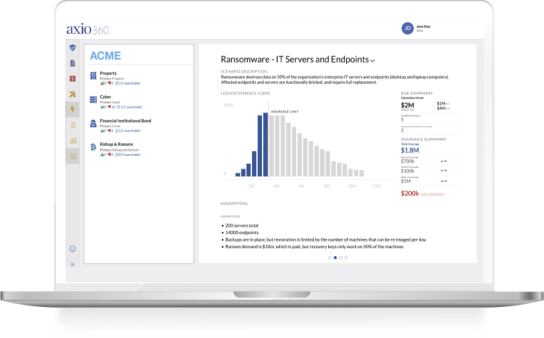
Axio360: The CISO’s tool for rapid cyber program maturity
Quickly understand gaps in your ability to comply with the new SEC cyber disclosure rules
Evolve the way you measure and communicate cyber risk and posture to increase the board’s preparedness and understanding of the cyber risk profile
Quantify your risk to understand the business impact of postural deficiencies
Sustain and improve the organization's posture by building a prioritized budget and plan and tracking your performance
Leverage cyber risk quantification to rapidly and effectively comply with cyber incident reporting rules